April Fools' Day pranks fade away quickly, but scammers never take a break.
Spring marks a peak period for cybercriminals. It's not due to negligence but because busy teams, juggling multiple tasks, can overlook subtle threats.
During hectic workdays, cleverly disguised scams can slip past even the most vigilant employees.
Below are three current scams targeting diligent professionals just like your team.
As you review these, consider: Does my team have the awareness to spot each one before it causes harm?
Scam #1: Fake Toll or Parking Fee Alerts
An employee receives a text similar to:
"You owe $6.99 for an unpaid toll. Pay within 12 hours to avoid extra fees."
The message names real toll providers like E-ZPass or SunPass matching their location. The small fee feels routine and unthreatening.
Distracted between meetings, they click on the link and pay—only to find out the link was malicious.
In 2024 alone, the FBI recorded over 60,000 reports of toll-related scam texts. By 2025, these fraudulent domains surged by 900%, signaling a lucrative scam industry.
Some are so convincing they even target states without toll roads. The low dollar amount and familiarity make these scams highly effective.
The safeguard: Authentic toll agencies never demand immediate payment via text. Encourage your team to avoid paying through SMS links, instead verifying charges through official websites or apps. Never respond to such messages, as replying confirms active numbers and invites further attacks.
Remember: convenience is the trap, and adherence to verified payment processes is your best defense.
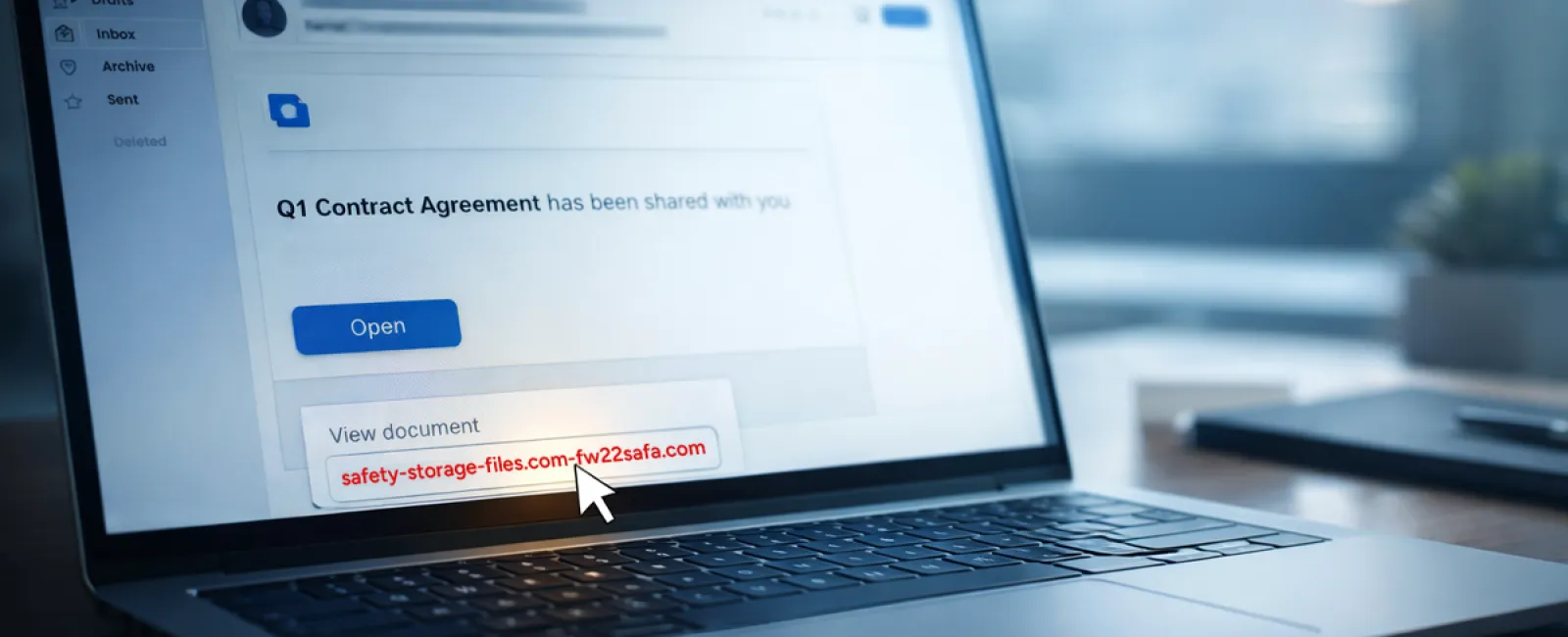
Scam #2: "Your File Is Ready" Phishing Emails
These scams blend seamlessly into daily workflows. An employee receives an email notifying them about a shared file—often appearing as a DocuSign contract, OneDrive spreadsheet, or Google Drive document.
The sender's details and formatting look legitimate, mimicking trusted platforms flawlessly.
When the employee clicks and logs in, they unknowingly hand over credentials, granting attackers access to your company's cloud environment.
Phishing attacks exploiting trusted platforms rose 67% in 2025, with Google Slides-linked scams spiking over 200% in just six months. Employees are seven times more likely to fall for links originating from OneDrive or SharePoint notifications than random emails.
Newer scams use compromised accounts to send legitimate notifications, making detection tougher as emails pass spam filters undetected.
Defense strategy: Train staff to avoid clicking unexpected file-sharing links. Instead, they should log in directly via platform portals to verify files. Additionally, restrict external sharing permissions and activate alerts for unusual login activity—measures your IT team can implement swiftly.
Consistent, cautious habits offer robust protection.
Scam #3: Sophisticated AI-Crafted Phishing Emails
Gone are the days of amateurish phishing emails full of typos and odd phrasing.
Today's AI-powered scams appear impeccably professional, referencing authentic company names, roles, and procedures—data pulled from LinkedIn and corporate websites.
A 2025 study revealed AI-generated phishing messages achieved a 54% click rate, over four times higher than human-crafted ones.
These emails target departments precisely — HR receives fake employee verifications, finance teams get fraudulent vendor payment requests. In recent tests, 72% of employees interacted with vendor impersonation emails, 90% more than other phishing types.
The emails are calm, professional, urgent yet subtle, mimicking normal business correspondence.
How to respond: Verify requests involving credentials, payments, or sensitive data through a separate communication channel like a call, chat, or in-person check. Always hover over senders' email addresses to confirm domain authenticity, and treat urgent messages with extra caution—they often signal risk.
True security is built on calm vigilance, not fear or haste.
Key Takeaway
These scams exploit familiarity, authority, timing, and the urge to act quickly.
The risk isn't careless employees—it's flawed systems that expect everyone to be perfect under pressure.
Remember: if one hurried click can cause major problems, the root issue lies in your processes, not your people.
And the great news is: processes can be improved.
Our Support Awaits
Business owners often don't want cybersecurity to become an overwhelming extra task or their sole responsibility.
They just want confidence that their company's safety isn't compromised.
If you're worried about your team's vulnerability—or know someone who should be—we're ready to help.
Book a clear and honest discovery call where we'll discuss:
- Current risks facing businesses like yours
- How vulnerabilities arise during routine tasks
- Effective strategies to reduce risk without hindering productivity
No pressure, no scare tactics—just straightforward guidance and options.
Click here or give us a call at (858) 538-4729 to schedule your free Consultation.
If this message isn't relevant to you, feel free to share it with someone who would benefit. Sometimes, knowing the warning signs is all it takes to turn a "near miss" into a safe outcome.